Infrastructure
This page documents VTLUUG's infrastructure post-CVL eviction.
Contents
Physical Infrastructure
NFS Hosts
- dirtycow - Primary NFS server, 8x2TB raidz2 array
VM Hosts
- meltdown - Primary VM/docker host
- spectre - Secondary VM/docker host, for example user VMs
- gibson - Secondary VM/docker host, Intel Arc A770, for GPU loads
- prospit - Secondary VM/docker host, GTX 1080, for GPU loads
Whit Cluster
- vesuvius - SAN/control plane, 8x12TB raidz2 array
- bastille (blades) - worker nodes
Routers
- shellshock - Whit router, 3 disk RAID1 array
- zerocool - McBryde router
All hosts are on our own 1 Gb/s port with shellshock, a gateway featuring ARP proxying, and full delegation of the 2607:b400:6:cc80/64 prefix.
Virginia Tech has started blocking inbound ports 22 and 3389 and outbound port 25 at the campus border, in a move echarlie is calling Cyber Auschwitz. Contact itso-g@vt.edu for firewall exceptions. When deploying new hosts, make ssh listen on both 2222 and 22. Acidburn currently listens on 3128 as well.
Other hosts
- joey used to be the router, but is no longer in use due to a failure of the single drive
- Wood is sitting in our rack turned off because we don't have a use for it currently. It is in a 4U case capable of fitting several GPUs.
- cyberdelia - OFF, 7x1TB raidz2 array, sitting on shelf instead of rack
- sunway and a SuperMicro server were all transferred to WUVT. Older hosts have either been thrown out or given to members.
See VTLUUG:Strategic_plan for things we plan to do in the future.
On the Network Architecture
Further Information: Infrastructure:Networking and Infrastructure:Network
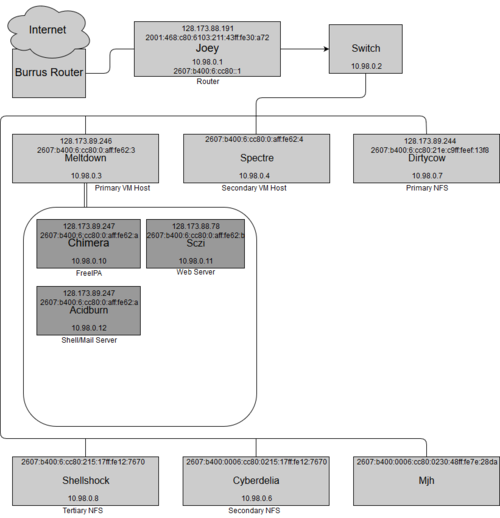
We currently have some services with public IPv4 address, and all hosts have an internal IPv4 address on the 10.98.x.x/16 subnet and an IPv6 address assigned via SLAAC.
In the future, VPN/Iodine should be used.
In theory, services can be provided via a hidden service such as Tor, but that introduces other complications. Alternately, services can require use of the VPN on acidburn, Iodine, or ssh tunnelling, although all of these limit usage to members with a shell account. All of these have the benefit of NAT transversal, however.
Services
Further information: Category:Services
- acidburn
- chimera
- FreeIPA
- Sczi
- Website
- hokieprivacy
- vtbash
- Main Site
- This wiki and Gobblerpedia
- dex, for authing with the wikis
- https://vtluug.org/users/~$user - User homepages
- 4get a metasearch engine
- Gitea a Github-esque git server with dex/LUUG OpenID auth
- element, a Matrix client
- slskd
- qbittorrent-nox
- bitwarden
- Website
- nikonwormhole
- AdGuard DNS blackhole
- dirtycow
- Storage for all primary services
- NFS - ZFS pool name is cistern
- meltdown
- VM host for above services
- scaryterry
acidburn and the website must be accessible through real services, and it is preferable other hosts are too. This means we must use our public IPv4 & IPv6 Addresses allotted by ECE.
Website details
Current Setup
All vtluug websites are run on nginx on sczi. These sites are currently functional:
- gobblerpedia.org
- hokieprivacy.org
- vtluug.org
- wiki.vtluug.org (redirects to vtluug.org/wiki/)
- bash.vtluug.org
- vtluug.org/users/~$user
All of these sites exclusively allow for the use of TLS connections. All services use automatically updated letsencrypt certs.
Main Page
The main VTLUUG page was scraped from the Internet Archive and added created as a github page at vtluug.github.io, and is reverse-proxied through sczi.
Wiki
The wiki currently runs fully on MediaWiki hosted on nginx using a modified version of the official mediawiki docker image. You can auth with the admin account, wiki-admin or a Google account. See note on Main_page about why LDAP isn't working yet.
Gobblerpedia
Runs on the same Mediawiki instance as this wiki. Similarly to LUUGWiki, only Google accounts or the admin user are supported logins.
Needs Restoration
These are VTLUUG services that haven't yet been properly restored:
- foodfor.vtluug.org - For Wadsworth's .pickfood and .foodvote commands. This is jpo's fault.
- tahoe.vtluug.org - mhazinsk's Tahoe-LAFS grid
- git.vtluug.org - git hosting; previously a redirect to gitweb with gitosis as the SSH backend
- gitweb.vtluug.org - git hosting; previously gitweb
- map.vtluug.org - OSM based map of VT
Historically
See Dead_projects for historic information
Goals
See VTLUUG:Strategic_plan#Web_Services for future goals involving web services
Addressing
VTLUUG currently has DNS with gandi.net. Message officers for access (please don't be scared :D).
We currently hold the IPv6 prefix 2001:470:8:6d9::/64 from HE's allocation due to our tunnel.
When CNS finally sets up prefix-delegation, we might be able to get something from 2607:b400::/32,
which is VT's largest allocation.
IF YOU CHANGE/ADD/REMOVE SOMETHING HERE CHANGE IT IN Inventory AND/OR Deprecated_Inventory TOO
This page describes specifics about VTLUUG's current network. For an overview, see Infrastructure:Networking
Addresses
| ECE DNS | VTLUUG DNS | IPv4 | Private Internal IPv4 | IPv6 |
|---|---|---|---|---|
| luug.ece.vt.edu | sczi.vtluug.org | 128.173.88.78 | 10.98.0.11 | 2607:b400:6:cc80:0:aff:fe62:b |
| N/A | scaryterry.vtluug.org | 128.173.89.163 | 10.98.0.22 | 2607:b400:6:cc80:0:aff:fe62:f |
| luug0.ece.vt.edu | dirtycow.vtluug.org | 128.173.89.244 | 10.98.0.7 | 2607:b400:6:cc80:21e:c9ff:feef:13f8 |
| luug1.ece.vt.edu | acidburn.vtluug.org | 128.173.89.245 | 10.98.0.12 | 2607:b400:6:cc80:0:aff:fe62:c |
| luug2.ece.vt.edu | meltdown.vtluug.org | 128.173.89.246 | 10.98.0.3 | 2607:b400:6:cc80:0:aff:fe62:3 |
| N/A | gibson.vtluug.org | 128.173.90.53 | 10.98.0.8 | 2607:b400:6:cc80:4a4d:7eff:fef9:8be5 |
| luug3.ece.vt.edu | chimera.vtluug.org | 128.173.89.247 | 10.98.0.10 | 2607:b400:6:cc80:0:aff:fe62:a |
| N/A | sphinx.vtluug.org | 128.173.88.255 | 10.98.0.20 | 2607:b400:6:cc80:0:aff:fe62:d |
| luug4.ece.vt.edu | mjh.ece.vt.edu | 128.173.88.104 | 10.98.0.254 | 2607:b400:0006:cc80:0230:48ff:fe7e:28da |
| luug5.ece.vt.edu | router.vtluug.org | 128.173.88.191 | 10.98.0.1 | 2001:468:c80:6103:211:43ff:fe30:a72 |
| N/A | nikonwormhole.vtluug.org | 128.173.88.135 | 10.98.0.21 | 2607:b400:6:cc80:0:aff:fe62:e |
| mirror.ece.vt.edu | N/A *Not sure if we can actually use this IP* | 128.173.88.82 | N/A | N/A |
| N/A | switch.private.vtluug.org (Internal v4 only) | N/A | 10.98.0.2 | N/A |
| N/A | spectre.vtluug.org | N/A | 10.98.0.4 | 2607:b400:6:cc80:0:aff:fe62:4 |
| N/A | cyberdelia.vtluug.org | N/A | 10.98.0.6 | 2607:b400:0006:cc80:0215:17ff:fe12:7670 |
| luug0.math.vt.edu | zerocool.vtluug.org | 198.82.185.170 | 10.98.4.1 | 2001:468:c80:6119:82c1:6eff:fe21:2b88 |
See Deprecated_Network for historical information.
VTLUUG
Addresses
IPv6
- Whit
- SLAAC on 2607:b400:0006:cc80::/64
- McB
- SLAAC on ???::/64
IPv4
- Whit
- 10.98.0.0/22: internal NAT
- Static IPs: 10.98.0.0/24
- DHCP: 10.98.1.0/24
- Reserved: 10.98.2.0/24
- Cluster: 10.98.3.0/24
- Iodine: 10.98.10.0/24
- we should renumber this to .2.0/24, probably, to stay within the new IPAM
- 128.173.88.1/22: publicly accessible hosts
- 10.98.0.0/22: internal NAT
- McBryde
- 10.98.4.0/22: internal NAT
- Static IPs: 10.98.4.0/25
- IPMI: 10.98.4.128/25
- DHCP: 10.98.5.0/25
- IPMI: 10.98.5.128/25
- Reserved: 10.98.6.0/23
- 198.82.185.129/22: publicly accessible hosts
All hosts have an internal address (static or DHCP) and some hosts also have a globally accessible address.
DNS
Shellshock and Zerocool also function as DNS servesr for their respective sites
- Whit
- 10.98.0.1
- 2607:b400:0006:cc80::1
- McB
- 10.98.4.1
VT's DNS
CNS maintains a few DNS servers on campus
- yardbird.cns.vt.edu, 2001:468:c80:2101:0:100:0:22, 198.82.247.34
- jeru.cns.vt.edu, 2001:468:c80:4101:0:100:0:42, 198.82.247.66
- milo.cns.vt.edu, 2001:468:c80:6101:0:100:0:62, 198.82.247.98
See Also
Contact Brandon Russell to get authoritative DNS entries added for *.ece.vt.edu- Brandon has left ECE -- the primary contact is Bruce Buskill, who may be less receptive to making DNS changes
- Contact Bill Reilly to get authoritative DNS entries assed for *.ece.vt.edu
- network liasions