Difference between revisions of "Virginia Tech Wifi (OLD)"
imported>Cov (→Connecting with Wicd) |
imported>Cov (→Connecting with Wicd: Added use of version template) |
||
| Line 190: | Line 190: | ||
==Connecting with Wicd== | ==Connecting with Wicd== | ||
| − | + | {{Version|Wicd 1.6.2.2 on Ubuntu 9.10 Karmic Koala}} | |
Wicd is an alternative to NetworkManager. It has proven to be more reliable than NetworkManager for a number of users. Unlike NetworkManager, to use Wicd, you do not need to convert the PKCS#12 certificate that CNS provides to a set of PEM certificates. If you need VPN or mobile broadband functionality, don't use Wicd, though. It doesn't have those features. Follow the instructions for converting the certificate and using NetworkManager instead. | Wicd is an alternative to NetworkManager. It has proven to be more reliable than NetworkManager for a number of users. Unlike NetworkManager, to use Wicd, you do not need to convert the PKCS#12 certificate that CNS provides to a set of PEM certificates. If you need VPN or mobile broadband functionality, don't use Wicd, though. It doesn't have those features. Follow the instructions for converting the certificate and using NetworkManager instead. | ||
Revision as of 18:57, 5 January 2010
Contents
Introduction
Since the fall of 2008, there have been two options for connecting to the Virginia Tech network by wireless card. One network, called VT-Wireless, operates by means of WPA2 Enterprise and is secured with EAP/TLS. The other network, called VT_WLAN, is an unsecured, captive portal wireless network. While connections to VT-Wireless are secure by default, and require no user authentication once set up, the setup has a number of steps. In contrast, setup for VT_WLAN network is negligible, but you will be required to manually authenticate each time you connect (although this can be scripted).
| VT-Wireless | VT_WLAN | |
|---|---|---|
| Secure (Encrypted) Connection | yes | no |
| Setup | involved | trivial |
| Authentication | automatic | manual |
VT-Wireless
The VT-Wireless network is secured by WPA with EAP/TLS encryption. This encryption mechanism is put in place through a certificate authentication mechanism.
Obtaining the VT-Wireless Certificate
Regardless of what program you use to make your connection, you will need to obtain your p12 certificate and password from CNS. Complete the form and download the p12 certificate file. Save the certificate password permanently and copy it for immediate use. You will need it in setting up your connection to VT-Wireless.
Choosing a Network Manager
NetworkManager is installed by default on Ubuntu and Fedora. As of fall 2009, it does not support the PKCS#12 format certificates that CNS provide out of the box, however. Converting the certificate requires some work, but the steps are outlined below. If you don't rely on NetworkManager for other kinds of connections like mobile broadband or VPN, or are having problems with NetworkManager, use Wicd instead. If you don't want or need a graphical interface, a WPA Supplicant configuration is also described below.
Connecting by NetworkManager
The setup for NetworkManager depends on your version of the software. Please follow the instructions appropriate to your version below. In GNOME, you can right-click the NetworkManager applet icon in the panel and select "About" to find the version of NetworkManager.
Ubuntu users: Version 0.6 ships with 8.04 Hardy Heron, 0.7 ships with 8.10 Intrepid Ibex and 9.04 Jaunty Jackalope, and 0.8 ships with Karmic Koala.
NetworkManager 0.7 and 0.8
Converting the certificate to PEM certificates and keys
NOTE: The following steps are only necessary to use NetworkManager 0.7 and 0.8. NetworkManager 0.6 has a more straightforward setup
You will need to convert the PKCS#12 (.p12) certificate into PEM formats. We will assume your downloaded p12 file is called netcert-1.p12 and that its password is netcertpasswd.
Open a terminal and cd to the directory that contains your .p12 file. Then issue the following commands:
openssl pkcs12 -in netcert-1.p12 -out vt_client_cert.pem -clcerts -nokeys openssl pkcs12 -in netcert-1.p12 -out vt_private_key.pem -nocerts
In each step, you will be prompted for the password (netcertpasswd) that you were issued along with your .p12 certificate. Right click and paste it in or press ctrl+shift+v if you're using the GNOME Terminal. Additionally, in the final step where you generate your private key, you will be asked to enter a password. Enter the same password that came with your p12
key.
Sources
Make sure you have the CA Certificate
Next, you will need to make sure you have the Thawte certificate authority certificate. In Ubuntu, you should be able to find this certificate at /etc/ssl/certs/Thawte_Premium_Server_CA.pem. If you can't find the certificate on your system, you can copy the text below and paste it into a new file of the same name.
-----BEGIN CERTIFICATE----- MIIDJzCCApCgAwIBAgIBATANBgkqhkiG9w0BAQQFADCBzjELMAkGA1UEBhMC WkExFTATBgNVBAgTDFdlc3Rlcm4gQ2FwZTESMBAGA1UEBxMJQ2FwZSBUb3du MR0wGwYDVQQKExRUaGF3dGUgQ29uc3VsdGluZyBjYzEoMCYGA1UECxMfQ2Vy dGlmaWNhdGlvbiBTZXJ2aWNlcyBEaXZpc2lvbjEhMB8GA1UEAxMYVGhhd3Rl IFByZW1pdW0gU2VydmVyIENBMSgwJgYJKoZIhvcNAQkBFhlwcmVtaXVtLXNl cnZlckB0aGF3dGUuY29tMB4XDTk2MDgwMTAwMDAwMFoXDTIwMTIzMTIzNTk1 OVowgc4xCzAJBgNVBAYTAlpBMRUwEwYDVQQIEwxXZXN0ZXJuIENhcGUxEjAQ BgNVBAcTCUNhcGUgVG93bjEdMBsGA1UEChMUVGhhd3RlIENvbnN1bHRpbmcg Y2MxKDAmBgNVBAsTH0NlcnRpZmljYXRpb24gU2VydmljZXMgRGl2aXNpb24x ITAfBgNVBAMTGFRoYXd0ZSBQcmVtaXVtIFNlcnZlciBDQTEoMCYGCSqGSIb3 DQEJARYZcHJlbWl1bS1zZXJ2ZXJAdGhhd3RlLmNvbTCBnzANBgkqhkiG9w0B AQEFAAOBjQAwgYkCgYEA0jY2aovXwlue2oFBYo847kkEVdbQ7xwblRZH7xhI NTpS9CtqBo87L+pW46+GjZ4X9560ZXUCTe/LCaIhUdib0GfQug2SBhRz1JPL lyoAnFxODLz6FVL88kRu2hFKbgifLy3j+ao6hnO2RlNYyIkFvYMRuHM/qgeN 9EJN50CdHDcCAwEAAaMTMBEwDwYDVR0TAQH/BAUwAwEB/zANBgkqhkiG9w0B AQQFAAOBgQAmSCwWwlj66BZ0DKqqX1Q/8tfJeGBeXm43YyJ3Nn6yF8Q0ufUI hfzJATj/Tb7yFkJD57taRvvBxhEf8UqwKEbJw8RCfbz6q1lu1bdRiBHjpIUZ a4JMpAwSremkrj/xw0llmozFyD4lt5SZu5IycQfwhl7tUCemDaYj+bvLpgcU Qg== -----END CERTIFICATE-----
Left-click the NetworkManager applet and select the VT-Wireless network.
You will see a prompt to configure the connection. First, from the Authentication drop-down menu, select TLS.
Next, fill in the rest of the options:
| Field | Value |
|---|---|
| SSID | VT-Wireless |
| Wireless Security | WPA & WPA2 Enterprise |
| Authentication | TLS |
| Identity | Your VT PID |
| User Certificate | /path/to/vt_client_cert.pem |
| CA Certificate | /etc/ssl/certs/Thawte_Premium_Server_CA.pem |
| Private Key | /path/to/vt_private_key.pem |
| Private Key Password | netcertpasswd |
Click "Connect" and you should connect to the VT-Wireless network.
NetworkManager 0.6
Left-click the NetworkManager applet and select VT-Wireless. You will be prompted to enter information about the connection. Here are the entries you should use:
| Field | Value |
|---|---|
| SSID | VT-Wireless |
| Wireless Security | WPA2 Enterprise |
| EAP Method | TLS |
| Key Type | Automatic (Default) |
| Phase2 Type | None (Default) |
| Identity | Your VT PID |
| Password | empty |
| Client Certificate File | (None) |
| CA Certificate File | (None) |
| Private Key File | netcert-1.p12 (the certificate downloaded from VT NetCert) |
| Private Key Password | netcertpasswd |
Connecting with Wicd
The following instructions were written for Wicd 1.6.2.2 on Ubuntu 9.10 Karmic Koala and may not work on other platforms or versions. If you would like to see additional coverage, please add it yourself or make a request on the wiki's wanted page.
Wicd is an alternative to NetworkManager. It has proven to be more reliable than NetworkManager for a number of users. Unlike NetworkManager, to use Wicd, you do not need to convert the PKCS#12 certificate that CNS provides to a set of PEM certificates. If you need VPN or mobile broadband functionality, don't use Wicd, though. It doesn't have those features. Follow the instructions for converting the certificate and using NetworkManager instead.
To install Wicd on Debian-based systems, run sudo apt-get install wicd. Installing it will uninstall NetworkManager.
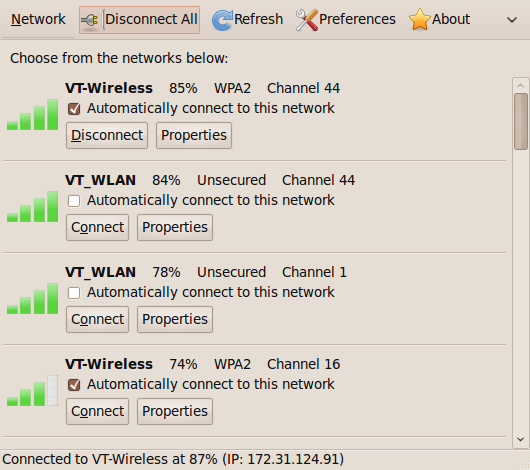
Open Wicd, either by left clicking the tray icon or by selecting Applications->Internet->Wicd Network Manager. Allow Wicd to scan the wireless networks then check the "Automatically connect to this network" checkbox by the topmost VT-Wireless entry. (You do not need to check the boxes for every VT-Wireless entry. The screenshot below was made from a working configuration that automatically checked all of them.)
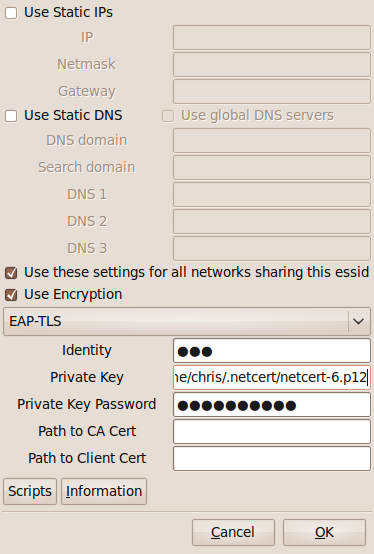
Click the "Properties" button of the topmost VT-Wireless entry and enter the following information:
- Check the "Use these settings for all networks sharing this essid" box.
- Leave the "Use Encryption" box checked.
- Select EAP-TLS from the encryption type dropdown menu.
- Enter your PID into the "Identity" box.
- Enter the path to your private key into the "Private Key" box, i.e.
/home/user/netcert/netcert-1.p12. - Paste the certificate password into the "Private Key Password" box.
Click "OK" and your computer should be all setup to use VT-Wireless.
Connecting by WPA Supplicant
WPA Supplicant is the preferred method of connection to WPA-secured wireless networks without a graphical interface. It supports PKCS#12 certificates.
Editing wpa_supplicant.conf
Add the following to your /etc/wpa_supplicant.conf file (if no file exists, create it):
network={
ssid="VT-Wireless"
key_mgmt=WPA-EAP
eap=TLS
identity="PID"
private_key="/PATH/TO/NETCERT.p12"
private_key_passwd="PASSWORD"
}
Replace PID with your actual PID (without any trailing @vt.edu),
/PATH/TO/NETCERT.p12 with the actual path to your certificate (you can
store it in /etc/netcert) and PASSWORD with the certificate password given to
you when you downloaded the certificate. Note the certificate used here
should be the original PKCS#12 file you downloaded. Reformatting the certificate
is only necessary for NetworkManager.
Running WPA Supplicant
Ubuntu
In Ubuntu, make sure to shut down NetworkManager with:
$ sudo /etc/init.d/NetworkManager stop
Next, issue the following command:
$ sudo wpa_supplicant -B -i wlan0 -D wext -c /etc/wpa_supplicant.conf
Confirm that you are associated with VT-Wireless
$ sudo iwconfig INTERFACE
where INTERFACE is your wireless card's device interface. Usually this is wlan0 but depending on udev and perhaps other system features, it might appear as ath0, eth1 or something else. Run sudo ifconfig -a to see all your interfaces listed.
If you have properly connected, you should see Access Point: followed by a MAC address (e.g., 00:0F:23:EA:4A:01). If instead you see Access Point: not associated, try the command again. If it still fails after a couple of seconds, bring down the interface and bring it back up:
$ sudo ifconfig INTERFACE down $ sudo ifconfig INTERFACE up
and re-issue the wpa_supplicant command.
Next, obtain an IP address. In Ubuntu, this is done with
$ sudo dhclient INTERFACE
If all goes well, you'll obtain an IP address. Otherwise, you'll receive a timeout for your DHCP request.
Gentoo
If you're already using wpa_supplicant, just restart your interface after editing wpa_supplicant.conf:
# /etc/init.d/wlan0 restart
This should connect you. If you're not using wpa_supplicant, you'll need to migrate from Wireless Tools to it in order to use WPA. Refer to the Gentoo documentation for a step-by-step guide to setting up WPA Supplicant.